Simultaneously, file also moves from user’s PCs to other pc methods that ask for it. This scenario works as two methods road – all file get convert into numerous small bits of information which come from user’s PCs however it releases after sending requests. Overlay P2P networks create a virtual Digital asset network on top of an existing infrastructure, such as the internet. This quantity shall be relayed and broadcast to each single node inside the network.
Unlocking Creativity: How Essay And Content Material Creator Assets Empower Writers
These identifiers can be, for instance, integers in the range [0, 2n-1], where n is a hard and fast quantity. Morpheus – Morpheus also used for file sharing and discovering peer to look shopper to Microsoft Windows that was designed and distributed by StreamCast group. BearShare – BearShare was launched by Free Peers, Inc for Microsoft Windows, after which it revised version of iMesh by MusicLAb. Peer to see architecture is utilizing of single software What is a P2P Cryptocurrency Exchange program where every bit of program performs their all tasks as each shopper and server along with comparable duties and capabilities.
- Each node serves as each a consumer and a server – they make use of the assets while simultaneously offering assets to others.
- This distributed nature of P2P networks provides several advantages, similar to elevated scalability, fault tolerance, and cost efficiency.
- To get round this, P2P networks use NAT traversal strategies, like UDP hole punching, to permit these restricted gadgets to attach.
- The utility is helpful to work in a decentralized pattern over the web.
What Are The Advantages Of Using P2p Community Technology?
Common routing algorithms embrace flooding, random walks, and greedy routing. The goal of those algorithms is to balance efficiency, scalability, and resilience in decentralized networks. Overlay networks create a further layer over the physical network to facilitate communication between nodes.
Information Management In Peer-to-peer (p2p) Networks
Unlike the unstructured community, the structured P2P community is organized into an association based on a distributed hash table (DHT). Unstructured networks have a tendency to make use of extra CPU and reminiscence, but they are less affected by the variety of friends joining or leaving the network (churn rate). The nature of the unstructured community makes it straightforward for localized optimizations, however the shared resources can be tough to find. The development of peer-to-peer (P2P) networks allowed all computers to be linked to each other and share assets, such as printer entry. Integration with blockchain technology, the rise of edge computing, and advancements in privacy and security measures will shape the evolution of P2P networks.
In other words, each computer on a P2P community becomes a file server in addition to a consumer. These apps find the friends with the data you want, share pieces of files, and examine that every thing is working accurately. It’s an efficient, flexible system used for all kinds of duties, from downloading information to supporting decentralized networks.
An overlay network is a virtual layer in P2P that connects devices even if they aren’t bodily linked. This layer additionally handles routing and knowledge exchange, ensuring the system stays related without having a central server. P2P networks exhibit robustness and fault tolerance due to their decentralized nature. Unlike client-server networks, the place the failure of a central server can disrupt the entire network, P2P networks can continue to perform even if particular person nodes fail or go away the network. Structured peer-to-peer (P2P) networks are the opposite of unstructured P2P networks i.e. nodes have a way to work together with one another in a extra organized manner. So one can achieve this through a well-organized structure that permits users to find and use files extra efficiently somewhat than searching randomly.
Unauthorized access is the largest foe of P2P blockchain networks and encryption, a deal maker. Overall, it’s simpler, and less power- and memory-intensive, to look a structured network for content material than an unstructured one. This contrasts with unstructured P2P networks, the place entire files may be stored on more than one node.

Therefore, P2P networks cowl a large areas of purposes together with file sharing, cryptocurrencies, and other features and making it as the basic a part of current distributed laptop methods. In a P2P network, every system can act both as a consumer and provider of resources. This decentralized nature provides several advantages, together with elevated scalability, fault tolerance, and lowered dependency on a single level of failure.

The blockchain protocol of peer-to-peer nodes will push the validated and verified transaction inside a specified block and the opposite user will have obtained the amount despatched by the first user. Bitcoin, for instance, is a peer-to-peer blockchain community that permits users to transact directly with one another without intermediaries. In peer to look networking, the customers make a trade-off by the phenomenon of “give and take”. As extra people continue to consume content, the content-serving capacity of P2P networks will potentially increase; that facility is not obtainable in a client-server structure. This attribute is an environment friendly advantage of employing P2P networks for the explanation that initial content material seller permits the configuration and working bills are very modest. Unlike an unstructured P2P network, the structured community is difficult to set up.
P2P networks energy distributed computing tasks, where people volunteer their gadgets to help clear up huge issues. Each gadget handles a small piece of a bigger task, like analyzing massive amounts of scientific data. By connecting 1000’s of computer systems, these networks create a robust useful resource that helps breakthroughs in fields like medical analysis. Traditional community purposes have been designed across the client–server model, by which providers are offered by dedicated nodes, often recognized as servers, and are consumed by passive end-nodes, known as shoppers. Typical examples include the World Wide Web, Electronic Mail, e-Commerce, and more recently Social Network platforms.
For instance, streaming platforms like Spotify leverage P2P networks to deliver their huge catalog of music to millions of users worldwide. By utilizing the computing resources of their customers, these platforms significantly scale back their infrastructure costs while providing seamless and uninterrupted streaming experiences. Normally, peer-to-peer communication is point-to-point, since the peers do not kind any major community. Hybrid peer-to-peer (P2P) networks combine P2P architecture with the client-server mannequin. This hybridization introduces a central server with P2P capabilities, proving advantageous for particular community eventualities.
It is important to weigh these disadvantages in opposition to the advantages of P2P networks when considering their implementation in varied purposes. By understanding the potential pitfalls, applicable precautions and security measures may be taken to mitigate these issues and ensure a protected and functional P2P community. These purposes present how adaptable P2P networks are, showcasing how they may be used to solve a range of issues in a selection of sectors by encouraging decentralization, useful resource sharing, and cooperative engagement.
Unstructured P2P networks are commonly used for file-sharing and content material distribution. For instance, platforms like BitTorrent utilize unstructured P2P networks to facilitate the sharing of enormous files among friends across the globe. This decentralized approach not only reduces the burden on particular person servers but in addition permits sooner and more efficient file transfers.
Security dangers, privacy considerations, and legal issues require careful consideration to ensure the integrity and trustworthiness of P2P networks. Implementing robust safety measures, educating users about best practices, and adhering to authorized frameworks are essential for maintaining a secure and accountable P2P community environment. This is an software that facilitates the person to switch the information free of price. The application is helpful to work in a decentralized sample over the web. The function of this protocol is to share the files, data distribution using peer to peer framework.
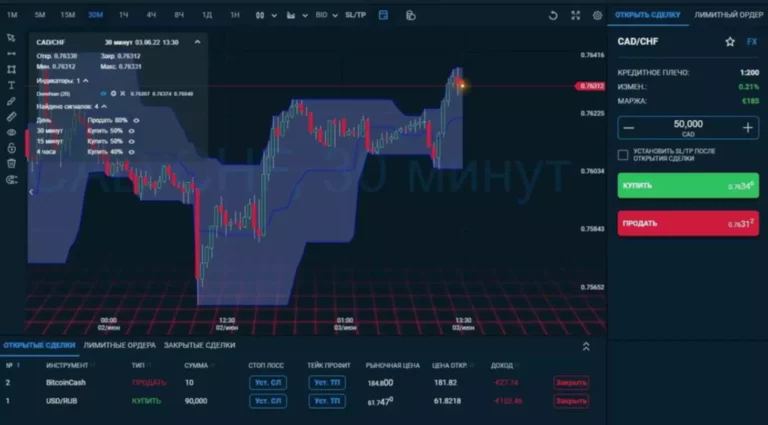
Start your own high-profit forex brokerage in just a few days or scale your existing business with the best-in-class forex software XCritical https://www.xcritical.in/. Get the perfect Turnkey Forex Solutions that will provide your business with efficiency, stability, and maximum profit.
